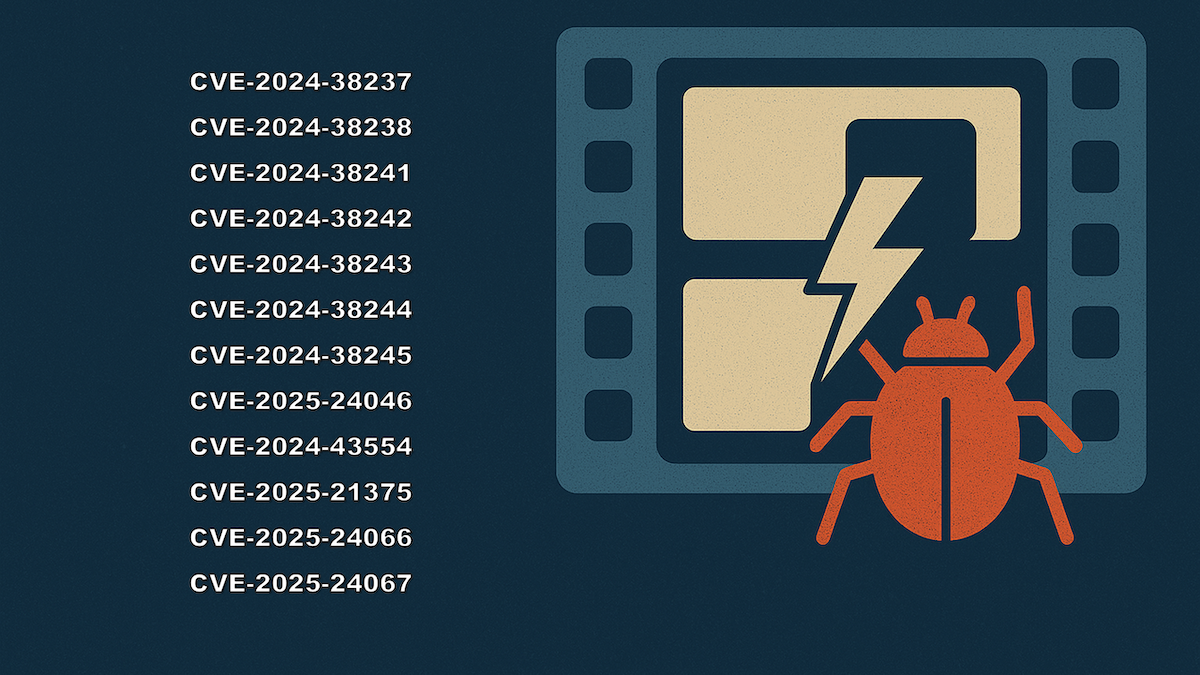
Frame by Frame, Kernel Streaming Keeps Giving Vulnerabilities
Angelboy
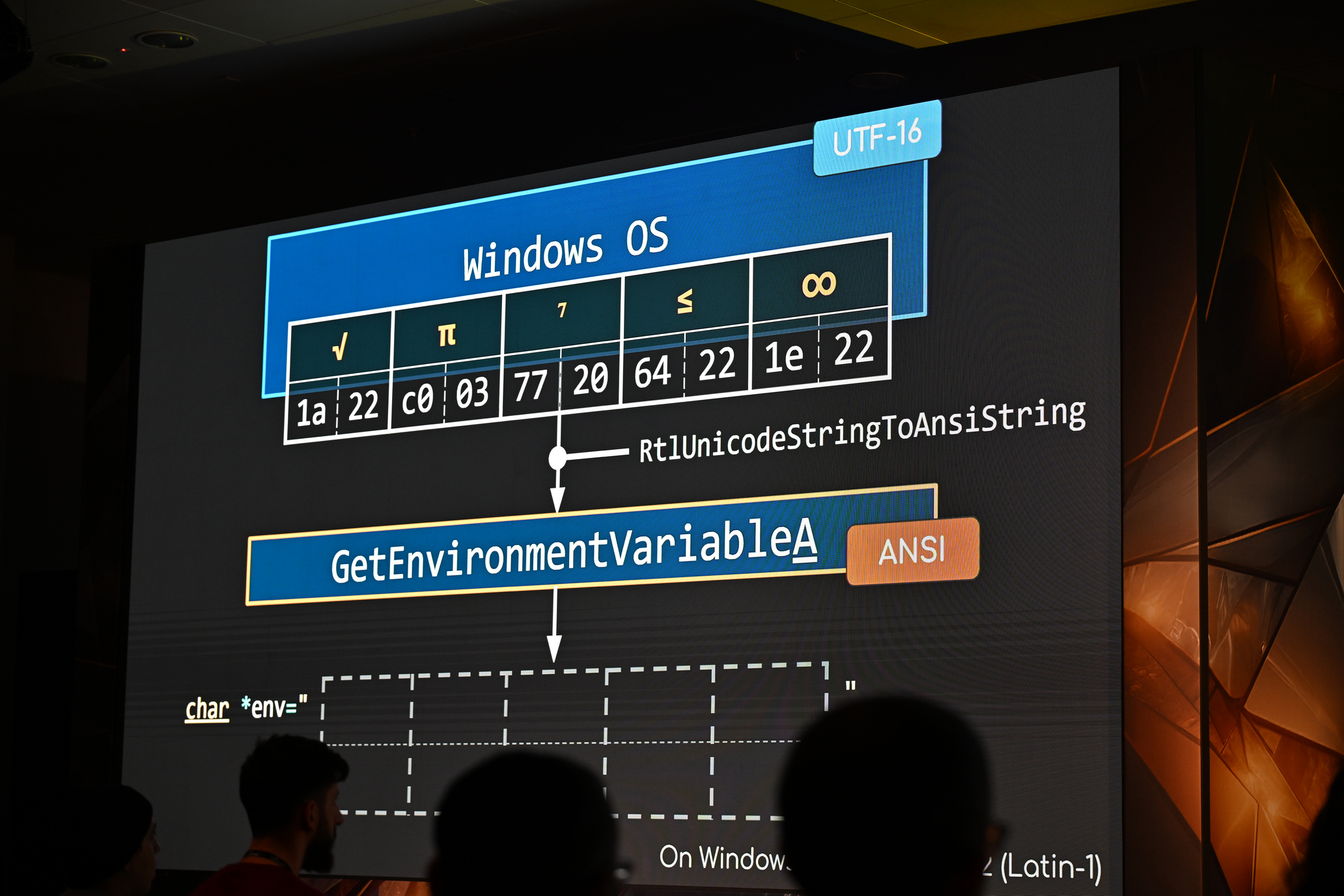
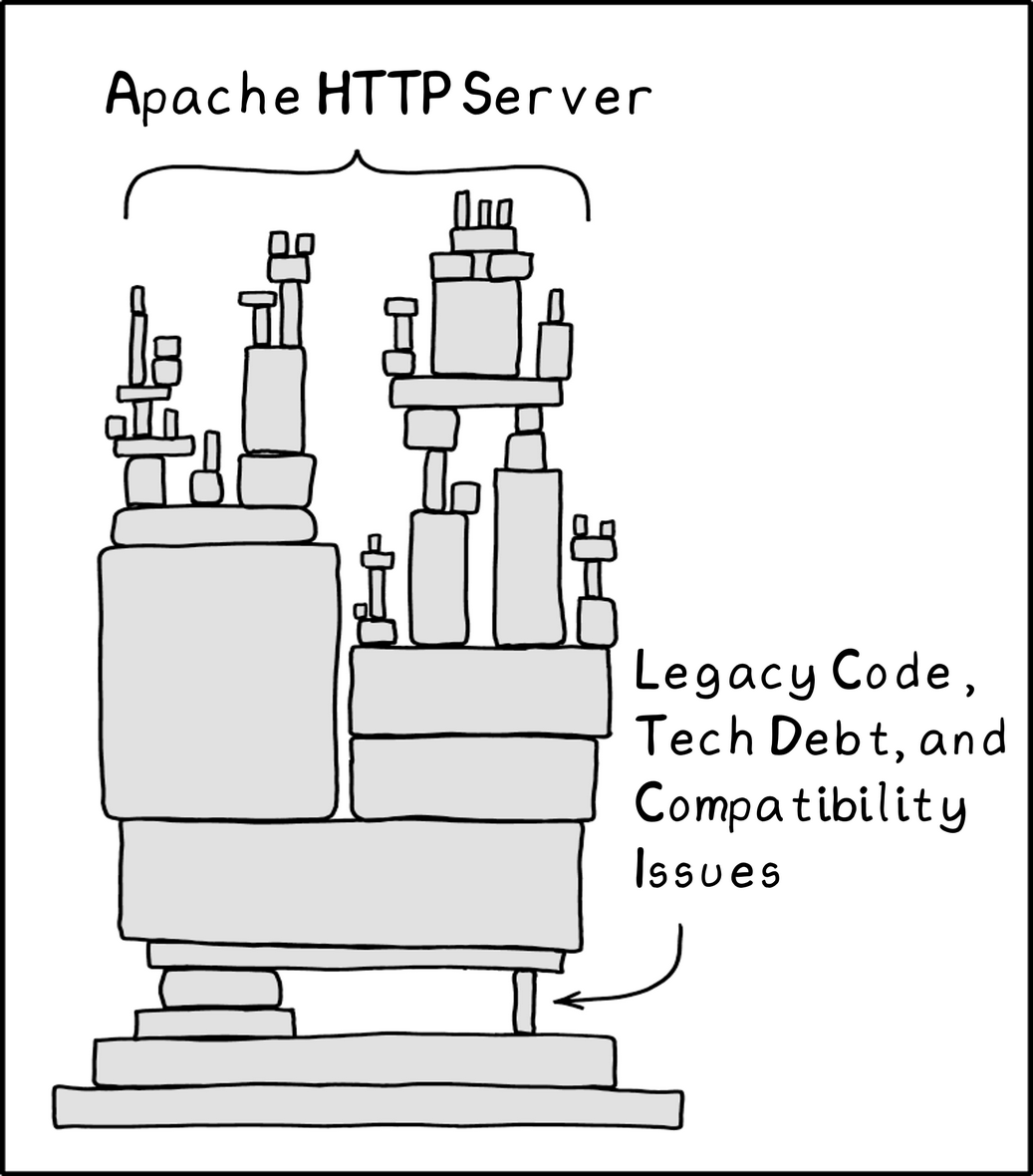
2025-05-17In-depth research into Windows Kernel Streaming vulnerabilities, revealing MDL misuse, buffer misalignment, and exploitation techniques used in CVE-2024-38238 and others.